 Eliza Gniadek
created
Eliza Gniadek
created
SPF, DKIM, and DMARC tools – what are they and why are they useful?
Back to list of articlesWithin a single second, as many as 3,500 emails are classified as spam. One type of email fraud is phishing, which is a fraudulent attempt to obtain sensitive information by posing as another entity.
At the start of 2018, anti-phishing software prevented over 3.7 million attempts to visit fake social media websites (60% of them were fake Facebook sites). Financial phishing is responsible for 43.9% of all attacks of this type (Kaspersky Lab).
This is why many email service providers, such as Gmail, use tools to protect email users against such attacks. These solutions require authentication (i.e. final proof) that you are the sender of the email (that the sender of the email is the person he or she claims to be). Emails secured in this way have a much better chance of reaching the recipients’ inboxes.
What are the SPF, DKIM and DMARC tools and how do they operate?
FreshMail uses three types of protection: SPF, DKIM and DMARC. Discover what these abbreviations stand for, how each security feature operates and what benefits it can give you.
Before you read the rest of the article, it is important to be familiar with the following terms:
Sender address “From” (header address) – you enter this address when creating an email campaign, and this address is seen by the recipients as “from”.
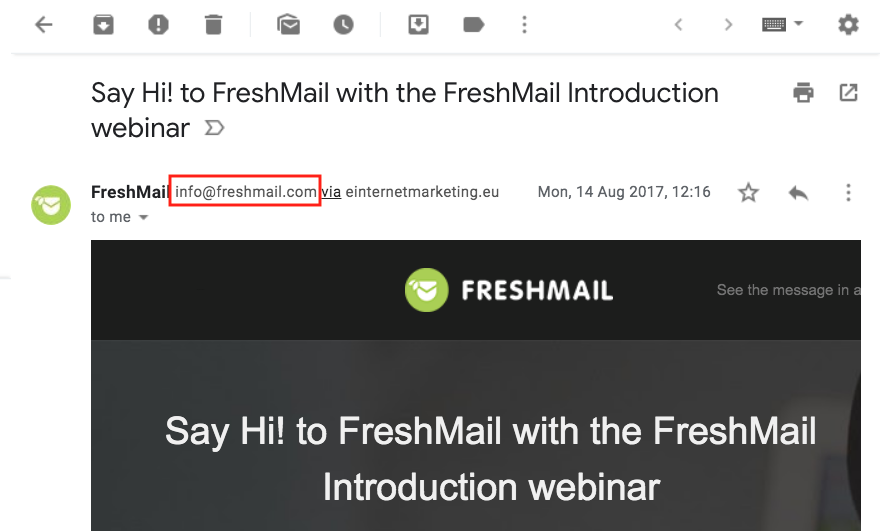
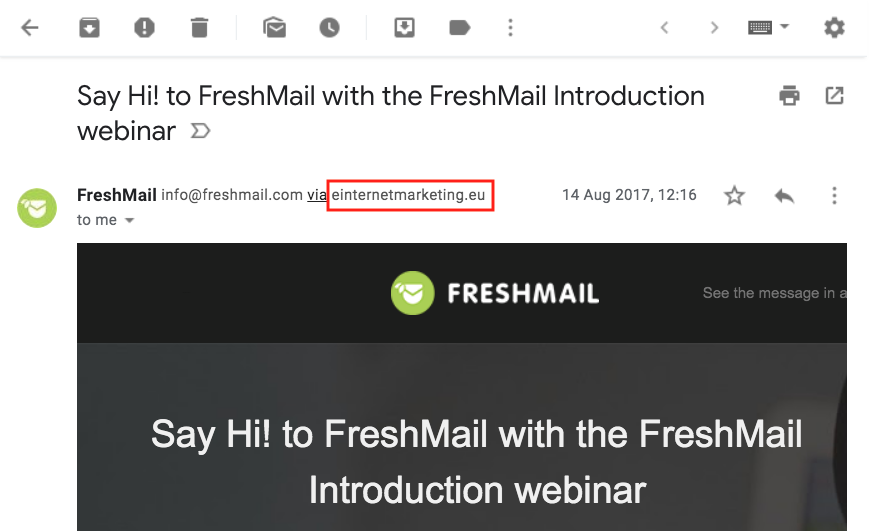
For example, when sending campaigns from FreshMail, we use the sender address in the freshmail.com domain – you can see it when you open our emails.
Sender address “Envelope From” (envelope address) – is set by our system. Most recipients do not see it (at the moment only Gmail users can see this address).
The screenshot below shows you that we used einternetmarketing.eu as the envelope address, which was one of several standard FreshMail domains.
SPF record
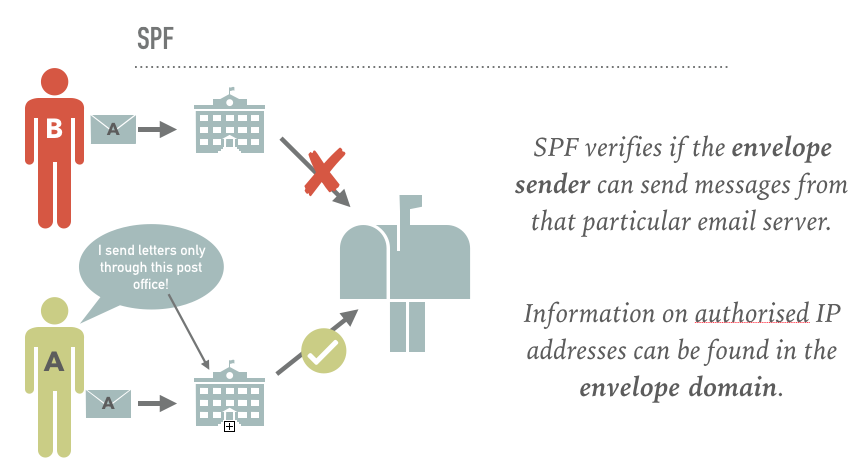
The Sender Policy Framework (SPF) record is an essential protection tool in the world of email marketing. The recipient’s email server checks if the IP address of the sender’s email server is authorised to send messages with the particular envelope domain. Information about which IP addresses of email servers can send messages from a particular envelope domain can be found in a special DNS record of that domain.
The Domain Name System (DNS) handles the database of all network addresses.
It could be compared to Yellow Pages or another company directory. The directory contains the names of companies and their exact contact details. If we only know the name of the company (i.e. domain name), we can use this company directory (i.e. DNS server) to obtain detailed contact data of that company (i.e. IP address).
By way of an example:
Let us imagine that John is a sender who decided to post letters to his clients. To prevent someone from impersonating him, he decides to authenticate his letters by sending them through only one designated post office, while informing all the recipients to reject letters sent from other post offices.
Consequently, if the recipient receives a letter with a stamp other than the one belonging to the chosen post office, the postman will not deliver it or he will throw it into a basket marked “spam”.
DKIM
DomainKeys Identified Mail (DKIM), in turn, can confirm the domain of both the envelope and the header sender. The mechanism digitally signs selected content of the email – it affixes a “padlock” which can be opened with the key contained in the domain – the same one used to send the email from the sender.
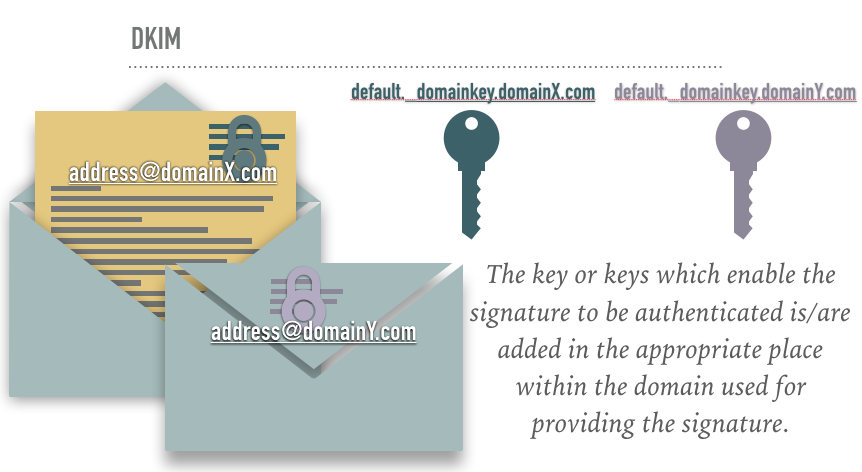
How does it work? When sending an email, an asynchronous encryption key (“padlock”), which is a private key, is placed in the header. When the recipient’s server receives such a message, it will ask the DNS for the second key – the so-called public key. If the public key matches the private key (our “padlock”), the message will be finally accepted.
DMARC
The Domain-based Message Authentication, Reporting and Conformance (DMARC) aims to confirm the sender’s domain using the previously discussed security measures (i.e. SPF or DKIM), and at least one of these mechanisms must confirm the domain of the sender’s header address in order for DMARC to allow the email to reach the recipient’s mailbox.
This can be compared to a doorman who lets into the building only those people who prove their identity using at least one method. Moreover, the doorman has detailed instructions on what to do if someone tries to bypass the procedure.
In certain circumstances, DMARC may only need SPF, but only if the client has a dedicated IP, has set up his own envelope sender domain and uses the same domain in the header address.
Why is DMARC so important?
SPF or DKIM tools acting independently of each other do not provide sufficient protection against spam. Although they allow senders to authenticate their domains, they do not specify exactly what the recipient’s server should do when this security measure is inadequate.
If you add DMARC to this configuration, you will instruct the servers receiving your mail to apply an appropriate policy against unauthorised emails:
- whether they will be rejected,
- or quarantined.
By using DMARC, you minimise the risk of anyone impersonating your company and fraudulently obtaining sensitive data, for instance, details needed for logging into a bank account.
With DMARC, you can increase the deliverability of your emails, as the sender. And the deliverability rate is a much more complicated issue than it seems.
According to research conducted by Return Path, only 83% of correct (not spam) emails reach their recipients in Europe. This means that 1 in 6 messages is blocked. The DMARC setting may make the email servers more favourable to your messages, as they will be able to identify and confirm the sender’s trustworthiness.
If there are any suspicions relating to fraudulent use of a domain, DMARC may also inform its owner. This means that if someone tries to impersonate you, you will have the opportunity to react – for instance, using legal means. DMARC is used by Google, AOL, Microsoft and Yahoo, among other email providers.
DMARC is currently becoming an increasingly popular solution and will soon be a market standard.
If you are sending messages using FreshMail and want to take advantage of SPF, DKIM or DMARC, but you are not sure how to do it – contact us: help@freshmail.com – We will be more than happy to help you!

